-
THE WALLET FOR EVERYONE: Ballet wallets are 100% offline. Storing your cryptocurrency assets in offline cold storage prevents unauthorized electronic access to the funds on your REAL Series wallets. Your funds cannot be electronically hacked.
-
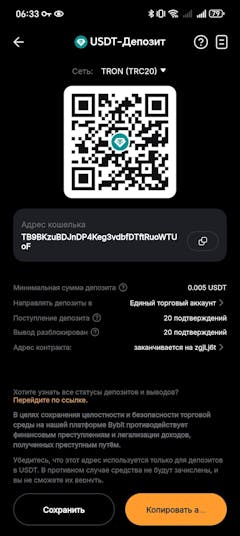
NO SETUP: REAL Series wallets come ready to use out of the box. Just scan a QR code to store your cryptocurrency and you’re all done!
-
NO MAINTENANCE: REAL Series wallets are physical wallets which, unlike electronic hardware wallets, don’t need to be maintained or electronically updated.
-
BALLET CRYPTO: The Ballet Crypto app allows you to easily view and manage your assets in real-time.
By intention, Ballet cryptocurrency wallets were designed to be without any computer chips or electronics circuitry. Computer chips and electronics circuitry present a vector for electronic or online hacking, and they usually also require constant maintenance and numerous firmware upgrades, leading to unnecessary complication and security risk. With the non-electronic Ballet wallets, you will never have to worry about any of these issues, which if severe, can lead to the user’s mistakes and loss of funds. REAL wallets were made with decentralization in mind, so only the end users have FULL and EXCLUSIVE control of their private keys, giving them full and unfettered access to their digital assets. Ballet’s wallet private keys are two-factor and made of two separate components, similar to 2-of-2 multisig private keys. Furthermore, we utilize a Two-Factor Key Generation (2FKG) production process, where the two critical private key components are generated in a geographically segregated, multinational private key production process. This patent-pending manufacturing process ensures the highest level security for our physical wallets. REAL Series wallets are made in accordance with BIP38 open industry standards. These tried-and-tested encryption and decryption algorithms further ensure the security of your funds, and assure you that you can still access your funds even if Ballet ceases operations. The encryption and decryption algorithms are non-proprietary, and we have open-sourced our software to ensure full access to the underlying decryption standards.